Hire a Nearshore GCP IAM Engineer: Secure, Scalable Cloud Access Control
- Leanware Editorial Team

- Mar 5
- 12 min read
Identity and Access Management is one of the most technically demanding disciplines in Google Cloud, and also one of the most underinvested. Organizations invest significantly in infrastructure but leave IAM in the hands of whoever is available, often a generalist who treats it as a secondary concern. Over-permissioned accounts, unmanaged service accounts, and access controls that were set up quickly and never revisited follow.
Hiring a dedicated GCP IAM engineer through a nearshore model is how security-mature teams address this gap without stretching their hiring budget.
Let’s break down what the role involves, when it becomes necessary, and how nearshore hiring fits into a mature cloud strategy.
What Does a GCP IAM Engineer Do?

A GCP IAM (Identity and Access Management) Engineer designs and manages access control in Google Cloud. They define who, including users and service accounts, can perform which actions on specific resources.
The role typically includes:
Assigning and refining IAM roles at the organization, folder, and project levels
Creating custom roles when predefined roles are too broad
Enforcing least-privilege access across teams and workloads
Managing service accounts and reducing key exposure
Configuring IAM policies and organization-level constraints
Ensuring audit logging supports traceability and review
Core Responsibilities in Google Cloud IAM
Day-to-day, a GCP IAM engineer works across role design and assignment (choosing between primitive, predefined, and custom roles and mapping them to job functions), organization policy configuration, audit log setup, regular access reviews, and conditional IAM policies using attribute-based conditions like IP range, resource type, or time of day.
Designing Least-Privilege Architectures
The principle of least privilege means that every user, service account, and application only holds the permissions it actually needs to do its job, nothing more. In practice, this requires a GCP IAM engineer to analyze workloads, map required API calls to the minimum set of permissions, and define custom roles where built-in predefined roles are too broad.
This directly reduces breach risk. If a compromised account only has read access to one Cloud Storage bucket, the damage is contained. If that same account has roles/editor on a project because someone granted it quickly and forgot about it, the exposure is your entire environment.
Managing Service Accounts and Workload Identity
Service accounts are one of the most abused surfaces in GCP: easy to create, easy to over-permission, and frequently forgotten. Common problems include service account keys exported to code repositories, accounts holding roles/owner at the project level, and accounts that no workload uses but still exist with active permissions.
A GCP IAM engineer moves teams toward Workload Identity Federation, which removes the need for service account keys entirely for workloads running on GKE, Cloud Run, or external systems via OIDC. This eliminates a whole class of credential leakage risk without adding operational complexity.
IAM in Multi-Project and Enterprise Environments
Enterprise GCP environments typically span dozens or hundreds of projects organized under folders and an organization node. IAM inheritance in this hierarchy means that a binding at the organization level propagates down to every folder, project, and resource underneath it. Misconfiguring a role at the org level is far more dangerous than a project-level mistake.
A GCP IAM engineer who understands this hierarchy designs access controls that take inheritance into account, avoids over-permissioning at high levels, and uses deny policies where appropriate to enforce hard boundaries regardless of what bindings exist lower in the hierarchy.
Why GCP Identity and Access Management Is Business-Critical
IAM is not an IT hygiene task. It directly affects security incidents, compliance audits, and access control issues in a GCP environment. Clear and well-structured IAM supports stable operations and consistent governance.
Security Risks of Poor IAM Configuration
Over 70% of cloud breaches involve compromised identities. IAM configuration defines how much access those credentials allow.
Common failure patterns include:
Granting Owner or other broad roles across projects for convenience
Shadow admins with effective administrative access through indirect role inheritance
Stale access from former employees or unused accounts
Misconfigured inheritance that spreads excessive permissions across the organization
When permissions are broader than necessary, a compromised account can access more resources than intended.
Compliance, Audit Readiness, and Governance
SOC 2, ISO 27001, and HIPAA require clear access control and traceable activity. Auditors review least-privilege implementation, access review processes, and logging of privileged actions.
GCP Cloud Audit Logs provide this record when configured correctly. An IAM engineer enables required logs, configures log sinks, and ensures data access logging is active where needed.
Without structured logging and access controls, audit preparation becomes more manual and time-consuming.
The Cost of Over-Permissioned Environments
Data breaches can be costly, particularly when sensitive data is involved. IAM misconfigurations are one contributing factor in many cloud incidents.
Over-permissioned environments also increase regulatory exposure. HIPAA and GDPR both include financial penalties for inadequate data protection, depending on the circumstances.
Correcting IAM weaknesses after an incident typically requires access reviews, policy restructuring, and remediation work. Establishing structured access controls earlier reduces that effort.
When Should You Hire a GCP IAM Engineer?
At a certain point, IAM becomes too complex to handle as a side responsibility. When access decisions start affecting security, compliance, or operational clarity, it usually requires someone who focuses on IAM directly.
Signs Your Organization Has IAM Gaps
Watch for these: multiple principals holding roles/owner at the project level, IAM bindings created manually through the console rather than code, no scheduled access reviews, service account keys rotated manually if at all, over 50 active service accounts with no ownership documentation, and open IAM findings in Security Command Center that have not been addressed in weeks.
Growing SaaS or Multi-Tenant Architectures
SaaS products running on GCP often serve multiple customers from shared infrastructure. IAM is the primary mechanism for enforcing isolation between tenants, controlling which service accounts can access which data, and ensuring that a bug or misconfiguration in one tenant's environment cannot affect another.
This requires purpose-built IAM architecture, not ad hoc permission grants.
Preparing for SOC 2, ISO 27001, or HIPAA
Compliance readiness requires demonstrable, auditable access control. This means documented role definitions, evidence of periodic access reviews, logging of all administrative activity, and controls that prevent unauthorized access to sensitive data.
A GCP IAM engineer can build this control environment from the ground up or remediate gaps in an existing one ahead of an audit.
Why Hire a Nearshore GCP IAM Engineer?
Nearshore hiring means engaging engineers in geographically close countries with overlapping time zones. For US and Canadian companies, this primarily means Latin America: Mexico, Colombia, Argentina, Brazil, and Chile.
The combination of time zone alignment, technical depth, and realistic cost makes it a practical choice for cloud security roles that require real-time collaboration.
Cost Comparison: Onshore vs Nearshore
A senior GCP engineer in the United States typically earns between $115k and $179k annually. That places monthly base compensation between $9.6k and $14.9k, excluding benefits, payroll taxes, and other employer costs.
A senior nearshore GCP IAM engineer in Latin America generally costs between $6.5k and $12k per month, depending on experience and engagement structure.
Below is a simplified comparison based on 2026 market ranges:
Profile | Approximate Monthly Cost |
Senior GCP IAM Engineer (US, onshore) | $9.6k-$14.9k |
Senior GCP IAM Engineer (Nearshore LATAM) | $6.5k-$12k |
Mid-Level GCP IAM Engineer (Nearshore LATAM) | $4.5k-$7.5k |
Actual costs can vary based on location, experience level, and market conditions.
Time Zone Alignment with US and Canada
LATAM engineers typically operate in EST, CST, or within one to two hours of US business hours. This means they join your standups, respond during your working day, and participate in incident response in real time.
For cloud security work, where a misconfiguration or active incident requires immediate communication and judgment calls, that overlap matters considerably more than it does for isolated development tasks.
Access to Senior-Level Cloud Security Talent
LATAM has a growing pool of engineers who hold Google Cloud Professional certifications, have built IAM architectures for enterprise environments, and have worked directly with compliance frameworks.
The quality argument for nearshoring is not just about cost. It is about accessing specialized talent that is often hard to find locally, particularly for niche disciplines like GCP IAM where senior practitioners are scarce in any market.
Technical Skills to Look for in a GCP IAM Engineer
When evaluating candidates, focus on strong GCP-specific IAM expertise, not just general cloud experience.
Skill Area | What to Look For |
GCP IAM Fundamentals | Resource hierarchy, role bindings, inheritance, permission evaluation |
Custom & Conditional Roles | Custom roles, CEL conditions, IAM deny policies |
Organization Policies | Org constraints and governance across folders and projects |
Service Account Security | Key restriction, rotation, scoped permissions |
Terraform (IaC) | Version-controlled IAM modules, reviewable changes |
Identity Federation | SAML/OIDC integration with Okta, Azure AD, or Google Workspace |
Monitoring & Controls | Security Command Center, audit logs, alerting |
VPC Service Controls | Protecting sensitive APIs and data boundaries |
Required Google Cloud IAM Expertise
A qualified GCP IAM engineer should be fluent in custom role creation, conditional role bindings using CEL (Common Expression Language), organization policies including custom constraints, IAM deny policies, resource hierarchy and inheritance behavior, and VPC Service Controls for protecting sensitive APIs.
Terraform and Infrastructure as Code
Manual IAM management does not scale and is not auditable. Any senior GCP IAM engineer should manage IAM bindings through Terraform using version-controlled modules that enforce consistent patterns, enable peer review of access changes, and make rollback possible.
Look for candidates who have written custom IAM modules, not just applied existing ones.
SSO, Identity Federation, and Zero Trust Models
An IAM engineer needs hands-on experience federating GCP with Okta, Azure AD, or Google Workspace via SAML or OIDC, configuring workforce identity federation, and implementing just-in-time access models aligned with zero trust principles.
Experience with Security Command Center and Audit Logs
Security Command Center surfaces IAM findings including service accounts with admin privileges and accounts with exported keys. An experienced IAM engineer uses SCC actively, triages findings, and configures log-based alerts for high-risk events like privilege escalation or large-scale permission grants.
Nearshore GCP IAM Engineer vs General DevOps Engineer
A common pattern in growing companies is assigning IAM work to the DevOps team. This works for basic setups but breaks down quickly as environments scale.
Why IAM Is Not Just "Another DevOps Task"
GCP IAM contains thousands of individual permissions across many services. Roles group these permissions, and inheritance applies them across the resource hierarchy. Conditional bindings and deny policies add additional layers that affect how access is evaluated.
A DevOps engineer can manage standard role assignments and service accounts. However, designing structured least-privilege access across multiple projects and maintaining it over time often benefits from focused IAM expertise.
Security-First vs Infrastructure-First Mindset
DevOps engineers typically focus on delivery, automation, and system reliability. Access decisions are often made in the context of enabling teams to move forward.
An IAM-focused engineer evaluates the same decisions through access boundaries, privilege scope, and reviewability. Separating these responsibilities helps maintain structured access control as environments grow.
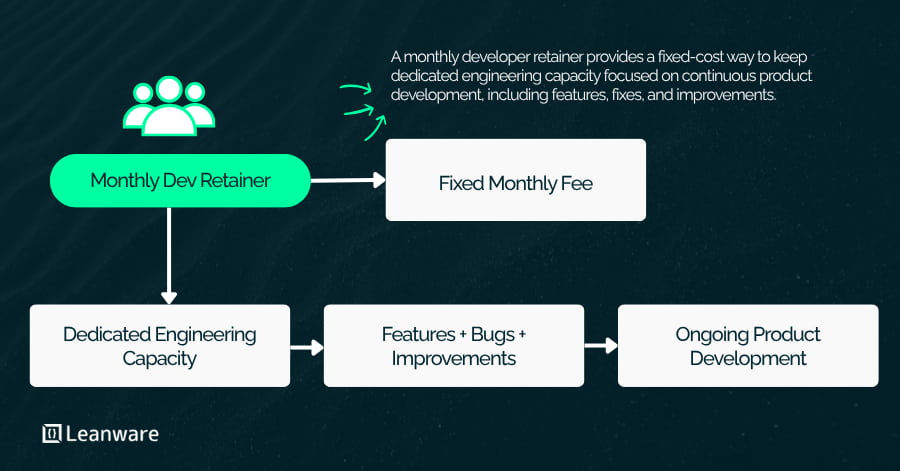
Engagement Models for Hiring a Nearshore GCP IAM Engineer
The right model depends on where you are in your cloud maturity and how much ongoing IAM work you have.
Staff Augmentation: The engineer embeds directly in your team, attends standups, and works in your tools. Best for organizations with a steady stream of IAM work who need domain ownership without adding headcount overhead.
Dedicated Security Engineer: Full ownership of your IAM environment with dedicated capacity. The right choice when you have identified IAM as an ongoing risk, not a one-time project.
IAM Audit and Remediation Project: A time-boxed engagement covering review of all IAM bindings, findings prioritization, and a remediation plan. A practical entry point before a compliance audit.
Long-Term Embedded DevSecOps Support: For mature engineering organizations, this positions the nearshore IAM engineer as a permanent function within the platform team, handling IAM code review, policy changes, and compliance requirements continuously.
When IAM Requires Dedicated Focus
IAM usually becomes a focus when access control starts affecting production design or compliance posture.
Scenario | IAM Focus |
Multi-tenant SaaS | Tenant isolation and controlled role bindings |
Fintech/Regulated | Dev-prod separation and restricted admin access |
Healthcare (PHI) | Least privilege and audit logging |
Enterprise Migration | Replacing broad legacy access models |
In each of these cases, IAM decisions influence how environments are structured and reviewed. At that stage, access control requires dedicated attention rather than occasional configuration changes.
Cost of Hiring a Nearshore GCP IAM Engineer in 2026
Compensation varies by region, experience, and engagement model. The ranges below reflect typical 2026 market estimates.
Role | Monthly Cost (USD) |
Senior GCP IAM Engineer (Nearshore LATAM) | $6.5k-$12k |
Mid-Level GCP IAM Engineer (Nearshore LATAM) | $4.5k-$7.5k |
Senior GCP IAM Engineer (US, base comp) | $9.6k-$14.9k |
US fully loaded employment cost may be higher when benefits, payroll taxes, and overhead are included.
ROI Compared to Onshore Hiring
The difference is primarily structural. Nearshore hiring often lowers monthly engineering spend at comparable seniority levels.
More importantly, dedicated IAM ownership reduces the operational time spent correcting access issues, preparing for audits, or restructuring permissions after growth. Over time, that consistency carries measurable value beyond salary alone.
Common Mistakes Companies Make with GCP IAM
IAM issues rarely come from complex edge cases. Most problems grow from basic decisions that were never revisited.
Using Owner Roles Excessively
roles/owner grants full control over every resource in a project, including the ability to change IAM policies and delete resources. When multiple team members hold this role by default, a single compromised account can result in total environment compromise.
Every principal should hold the minimum role that allows them to do their job, with Owner reserved for documented break-glass scenarios only.
Poor Service Account Management
Common service account issues include:
Exported JSON keys stored in repositories
Accounts created for short-term tasks and never removed
Project-level Editor roles assigned for convenience
A structured approach replaces long-lived keys with keyless authentication where possible, narrows service account roles, and includes periodic review of unused accounts.
Ignoring Organization Policies
Organization policies enforce hard constraints across your GCP environment regardless of project-level IAM bindings. Without them, developers can create resources that violate your security posture even when their IAM roles are well-scoped.
Managing org policies deliberately is governance work that requires someone who understands how constraints propagate through the resource hierarchy.
Why Specialized Cloud Security Talent Matters
Many organizations identify identity and access security as a primary cloud risk, yet IAM often remains a secondary responsibility.
GCP IAM includes detailed permission logic, inheritance rules, and policy constraints. Maintaining structured access control over time benefits from focused ownership rather than occasional configuration updates.
Find a Nearshore GCP IAM Developer
Hiring for IAM is about determining whether the engineer has designed and maintained access control in GCP at scale. The role requires real ownership of permission structures across projects, not just assigning roles in the console.
How to Vet the Engineer
Certifications indicate exposure to the subject, but experience becomes evident in how candidates describe their past work.
Ask them to explain:
An IAM structure they built across multiple projects
How they reduced broad roles like Owner or Editor
How they handled service accounts in CI/CD or GKE
Why they created specific custom roles
How IAM changes are managed through Terraform
If possible, review Terraform code they have written for IAM. Well-structured modules and consistent role patterns often reflect direct experience managing access at scale.
Questions to Ask Before Hiring
Use scenario-based questions:
How would you review IAM across 50 GCP projects?
What would you check before removing a long-standing roles/owner binding?
How do you manage service account keys for workloads outside GCP?
How do you control IAM changes in a code review process?
Look for structured, step-by-step answers grounded in real environments.
IAM rarely breaks in obvious ways. It weakens over time if no one maintains it deliberately. Consistent ownership keeps access structured and controlled.
Getting Started
IAM forms the base of your cloud security model. If permissions are loosely structured, other controls become harder to enforce and review. Addressing IAM early, or revisiting it as environments grow, keeps access predictable and auditable.
Nearshore hiring provides access to experienced GCP IAM engineers at a different cost structure than typical onshore roles. With consistent ownership, IAM becomes structured, reviewed, and maintained rather than adjusted reactively.
Connect with our team today to discuss how a nearshore GCP IAM engineer can bring structure and consistency to your Google Cloud access model.
Frequently Asked Questions
What does a GCP IAM Engineer do?
A GCP IAM engineer designs and manages access control in Google Cloud. They define roles, configure policies, manage service accounts, and structure permissions across organizations, folders, and projects. Their goal is to enforce least-privilege access and maintain consistent governance as environments grow.
Why is IAM important in Google Cloud?
IAM determines who can access resources and what actions they can perform. Poorly structured permissions increase the risk of unauthorized access, accidental changes, and compliance gaps. Well-designed IAM keeps access controlled and reviewable.
When should a company hire a GCP IAM Engineer?
Organizations typically bring in a dedicated IAM engineer when they operate multiple GCP projects, prepare for SOC 2, ISO 27001, or HIPAA, scale a SaaS platform, handle regulated data, or recognize that access control has grown beyond ad hoc management.
What is the difference between a GCP IAM Engineer and a DevOps Engineer?
A GCP IAM engineer focuses specifically on access control, identity federation, and permission governance. A DevOps engineer concentrates on CI/CD pipelines, infrastructure automation, and deployment workflows. IAM work requires deeper focus on security boundaries and compliance alignment.
What skills should a Nearshore GCP IAM Engineer have?
They should have strong expertise in GCP IAM, including custom roles and conditional policies, experience managing IAM through Terraform, knowledge of SSO and identity federation, familiarity with Security Command Center and audit logging, and hands-on experience implementing least-privilege access.
How much does it cost to hire a Nearshore GCP IAM Engineer?
In 2026, a senior nearshore GCP IAM engineer typically costs between $6.5k and $12k per month, depending on experience and engagement structure. Rates vary by region and scope of responsibility.
What are the risks of poor IAM configuration in GCP?
Common risks include overly broad roles, unintended administrative access, dormant accounts with active permissions, failed compliance reviews, and accidental deletion of critical resources. Most issues stem from permission sprawl over time.
Can a Nearshore GCP IAM Engineer help with compliance?
Yes. An IAM engineer can structure access controls, enable and organize audit logging, configure organization policies, and support access review processes that align with frameworks such as SOC 2, ISO 27001, and HIPAA.
What is least-privilege access in GCP?
Least-privilege access means granting users and service accounts only the permissions required for their specific tasks. This reduces the impact of compromised credentials and limits unintended changes.
Is hiring nearshore secure for cloud security roles?
Yes, when access is managed properly. Nearshore engineers operate within your GCP environment under your IAM controls. Security standards and compliance processes remain defined and enforced by your organization.




.webp)